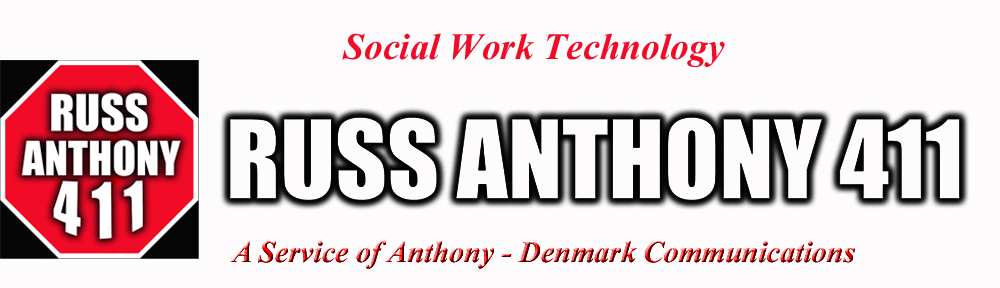
Julius Witherspoon and Lee Stewart of Metropolitan Social Services in Nashville, Tennessee speak about the growth of the elderly population and ways agencies can meet this need. This video shows excerpts from their presentation, “Increasing Need for Home and Community Based Services for Seniors and Disabled Adults” at the TCSW Middle Region Fall Conference on November 2, 2012. Video by Russ Anthony 411 for Anthony-Denmark Communications.
Tag Archives: technology
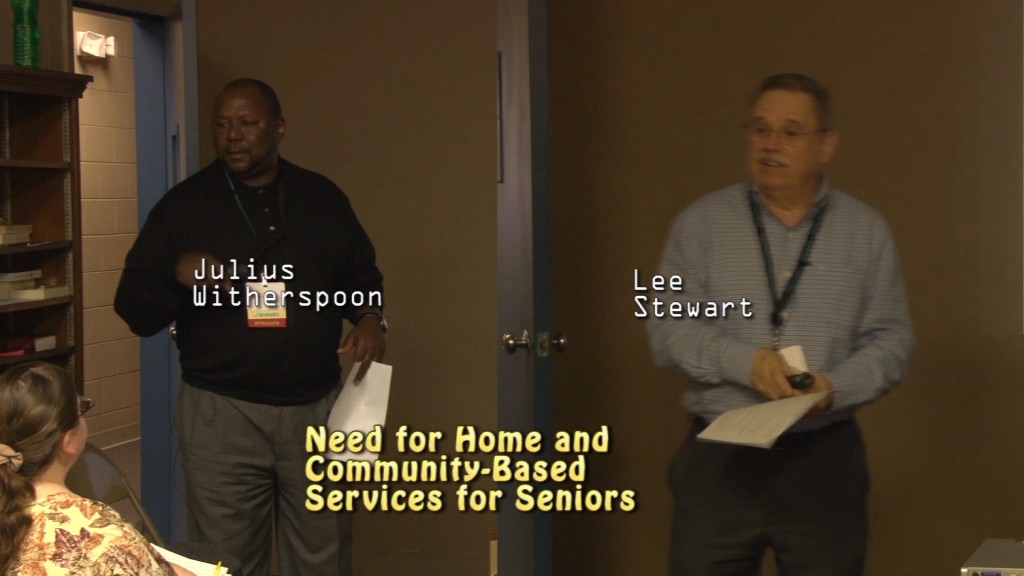
Advocacy
“You are an advocate”, says advocacy veteran Gordon Bonnyman from the Tennessee Justice Center. He speaks to the audience about the qualities needed for being an effective advocate for people and causes. These excerpts are taken from his presentation “The Whys and Wherefores of Advocacy” at the TCSW Middle Region Fall Conference on November 2, 2012. Video by Russ Anthony 411 for Anthony-Denmark Communications.
Poker Run – Riders For Homes
-
 Bikers participate in the Poker Run by traveling to arranged locations to pick cards to determine who will have the winning hand at the end. It is all for fun and a good cause as these bikers help to raise money to support services for the homeless in Tennessee. This video captures the first and last stop at Boswell’s Harley-Davidson and at Arrington Vineyards. Watch for short scenes from the concert that followed. Click here to watch the video online. Produced by Russ Anthony 411 for Anthony-Denmark Communications.
Bikers participate in the Poker Run by traveling to arranged locations to pick cards to determine who will have the winning hand at the end. It is all for fun and a good cause as these bikers help to raise money to support services for the homeless in Tennessee. This video captures the first and last stop at Boswell’s Harley-Davidson and at Arrington Vineyards. Watch for short scenes from the concert that followed. Click here to watch the video online. Produced by Russ Anthony 411 for Anthony-Denmark Communications.
Online Vote #4
Please click here to watch and my vote on my Anthony – Denmark end logo 4 on You Tube. Thank you.
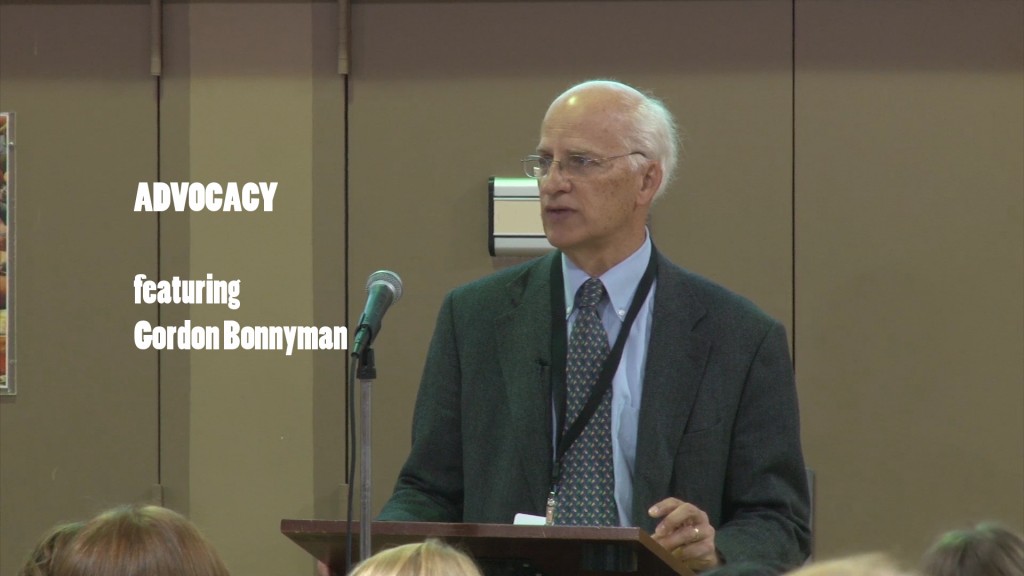
Evolution of Communication – Pt. 7
 Text messages are expected to be short and to the point. Click here to watch part seven of the Evolution of Communication video series from Anthony-Denmark Communications. Many teenagers and young adults rely on text massages more that actually talking on their smart phones. Watch as Nicholas Holland, CEO of CentreSource Interactive Agency, explains the emergence of text messaging in Evolution of Communication. This is a series of short videos that explains how humans have communicated since the beginning of time. In Part Seven: “Text Messaging”, Nicholas explains how text messaging improved communication with the ability to send and receive of highly relevant information quickly. Evolution of Communication – it’s something to talk about.
Text messages are expected to be short and to the point. Click here to watch part seven of the Evolution of Communication video series from Anthony-Denmark Communications. Many teenagers and young adults rely on text massages more that actually talking on their smart phones. Watch as Nicholas Holland, CEO of CentreSource Interactive Agency, explains the emergence of text messaging in Evolution of Communication. This is a series of short videos that explains how humans have communicated since the beginning of time. In Part Seven: “Text Messaging”, Nicholas explains how text messaging improved communication with the ability to send and receive of highly relevant information quickly. Evolution of Communication – it’s something to talk about.
Coming soon: Part 8: Instant Messaging
New Section: External Resources
Just added to RussAnthony411.org is a collection of links to other information for about technology and social work. You can find the list by clicking here or by going to the Social Work Technology page at the top of this site and look for “External Resources”. This additional reading material demonstrates some of the ways that technology is advancing social work on various levels. Your input is greatly appreciated.
Five Steps for A Social Work Technologist
Many social workers are adept in using technology to improve the lives of their clients and agencies. If you are a social worker that enjoys using technology, this is encouragement to consider becoming a social work technologist. While it may not be an official position, it is a needed position in many organizations. Here are five realistic things you can do to become a social work technologist in your workplace:
 1) Talk to coworkers and colleagues about your tech skills and share information. Share experiences about using technology from your department or agency with others. Be a source of support. Gain support and learn from others.
1) Talk to coworkers and colleagues about your tech skills and share information. Share experiences about using technology from your department or agency with others. Be a source of support. Gain support and learn from others.
2) Let your boss/supervisor know that you have an interest in serving clients through the use of technology. Give examples or suggestions to improve the use of the computer network or changes to the client data base. Be realistic and practical for a better chance of a positive outcome.
3) Focus your intent to use technology around improving the lives of customers and/or improving the success of the organization. Most social agencies are over burdened. Look for ways that can have benefits towards clients or save the organization time/money.
4) Get noticed. Put your technology skills on display. Not in a selfish way, but in a manner that gets the higher-ups in your agency to expand their view of what social workers can do. Especially, if you work in an environment where the executives graduated from school before the Internet or personal computers.
5) Do your job. While this may seem obvious, you will be in a better position to state your case for becoming involved in your agency’s technology efforts if you are maintaining your caseload or primary work responsibilities. Demonstrating transferable skills such as organization and attention to detail will serve you well.
Doing these five things will put you on the road to becoming a social work technologist. From there, your mission will be to help others to take the same steps. I look forward to hearing about the technology efforts other social workers have made and are making. This site bears the phrase, “The Home of Social Work Technology”. I know that others are doing similar work from what little I have encountered. I do not know how large of a number there is of other technology-skilled social workers. However that number will surely increase as the younger social workers enter the workforce. By strengthening social work technology today, we can do our part to see that social work is being performed by social workers in the future.
Advancing Social Work Technology
Now is the time for technology-minded social workers to mobilize and unite. A call is being made for Social Work Technologists to improve the lives of clients by advancing our technical skills. For those looking for extra credentials, there is no exam or certification. However, you will be armed with skills that are greatly needed in the workplace for many social workers. Social workers everywhere need to stand on their keyboards and shout it out on Twitter, Facebook, Linked In, etc. that we can be trusted to use technology to serve our clients. For too long we have stood by and watched while computer and information technology professionals have directed the course of direct services to customers. (This is not written to antagonize those professionals but to work toward a better partnership for the welfare of the recipients of social and human services).
 Social workers know how to use technology to improve the lives of people and society. Yet, the very nature of a social worker’s job can be severely altered by a computer analyst without a clear concept of the work being done. This is not the fault of the tech department but an indication that the powers that be see social workers as lacking these needed technology skills. If we are not careful, every step from intake to case closure will be automated without input from the staff who know the clients.
Social workers know how to use technology to improve the lives of people and society. Yet, the very nature of a social worker’s job can be severely altered by a computer analyst without a clear concept of the work being done. This is not the fault of the tech department but an indication that the powers that be see social workers as lacking these needed technology skills. If we are not careful, every step from intake to case closure will be automated without input from the staff who know the clients.
This is not a selfish plea about saving social work jobs but a plea nonetheless to motivate and encourage social workers everywhere to take a stand and realize that many of our agencies can better if social workers utilized technology in the performance of job duties. Our clients will be that much better off.
Technology – A Blessing, A Curse with Lowell Perry, Jr.
 This is additional footage from Lowell Perry, Jr.’s closing presentation at the TCSW Conference in Franklin, Tennessee on April 6, 2011. Mr. Perry speaks about the advantages and disadvantages of life with cell phones and mobiles devices. He describes us as being tethered to technology. He also offers some insight on the importance of valuing one-on-one communication and to remember that there are times, “to put the phone down and acknowledge the person in front of us”. Click here for the video or go to the RussAnthony411 You Tube channel at www.y0utube.com/user/russanthony411 .
This is additional footage from Lowell Perry, Jr.’s closing presentation at the TCSW Conference in Franklin, Tennessee on April 6, 2011. Mr. Perry speaks about the advantages and disadvantages of life with cell phones and mobiles devices. He describes us as being tethered to technology. He also offers some insight on the importance of valuing one-on-one communication and to remember that there are times, “to put the phone down and acknowledge the person in front of us”. Click here for the video or go to the RussAnthony411 You Tube channel at www.y0utube.com/user/russanthony411 .
Spiritual Technology Advice: Keep Your Oil Lamps Trimmed
( The use of The Bible passages in this post is to show how wisdom through out the ages has applicability to technology life in 2011. These verses are repeated with respect and reverence).
If you are surfing the Internet for downloads, making a copy of a flash drive file or using wireless in your home or business read this verse from the New Testament and apply it to your use of technology.
1 “At that time the kingdom of heaven will be like ten virgins who took their lamps and went out to meet the bridegroom. 2 Five of them were foolish and five were wise. 3 The foolish ones took their lamps but did not take any oil with them. 4 The wise ones, however, took oil in jars along with their lamps. 5 The bridegroom was a long time in coming, and they all became drowsy and fell asleep.
6 “At midnight the cry rang out: ‘Here’s the bridegroom! Come out to meet him!’7 “Then all the virgins woke up and trimmed their lamps. 8 The foolish ones said to the wise, ‘Give us some of your oil; our lamps are going out.’9 “‘No,’ they replied, ‘there may not be enough for both us and you. Instead, go to those who sell oil and buy some for yourselves.’
10 “But while they were on their way to buy the oil, the bridegroom arrived. The virgins who were ready went in with him to the wedding banquet. And the door was shut.11 “Later the others also came. ‘Lord, Lord,’ they said, ‘open the door for us!’12 “But he replied, ‘Truly I tell you, I don’t know you.’13 “Therefore keep watch, because you do not know the day or the hour”. (NIV)
Always Be on Guard
Regardless of what your web browser claims, there is no real “safe search” setting. If you want to truly be free of identity theft hackers – pull the plug on the Internet. Even then you may have previously, and unknowing, downloaded a virus or trojan that is hiding in your computer just waiting for the opportunity to strike. For every identity theft program or firewall setting there is a crook somewhere whose sole purpose is to find a weakness in that program or setting. Life lesson: the security companies and the hackers have a shady backroom, cigar-filled, you-scratch-my-back-and-I’ll-scratch-yours, underhanded agreement. They make work for each other. Some times it is obvious. You know, when the warning comes on your screen, ” You have a virus!! Click here for our virus protection program”. They should know, they created the virus too. In the 40’s we called this the Mafia and extortion. Even the honest security companies know that if they cured “computer cancer” today they would be out of a job tomorrow. Viruses and worms are good for business.
“But while they were on their way to buy the oil…”
I do not mean to paint the picture that all is lost. There is something that you can do. If you are going to be on the Internet, the time to get a virus protection program is before, not after, a virus is detected. Repeat, the time to get a virus protection program is before, not after, a virus is detected. Sure the cards are stacked against the uninformed Internet user – just don’t be uninformed.
Here are some things you can do:
- Learn about net security. There are plenty of useful web sites where you can find this information. You can start by making a point to checkout information from your internet provider. Just be sure that you also use other sources by doing a web search. Do not rely on one source for your information.
- Establish ground rules for children you are using the Internet in your household. Monitor what sites they visit. Talk among others in your household or office about web security.
- Prevention + pro-activity = protection. Do not got out to buy your oil (virus protection program and knowledge about web security) only to find out that is too late. However, if you suffer damage from such an experience – treat it as a lesson learned. Be better prepared in the future. Talk to other Internet users about what you have learned.
Keep watch because you do not know…. That’s always been good advice.
By the way, admitting that something is hard to do is not a substitute for trying to do it.
Russ